Get ready for a facepalm: 90% of credit card visitors at this time use the very same password.
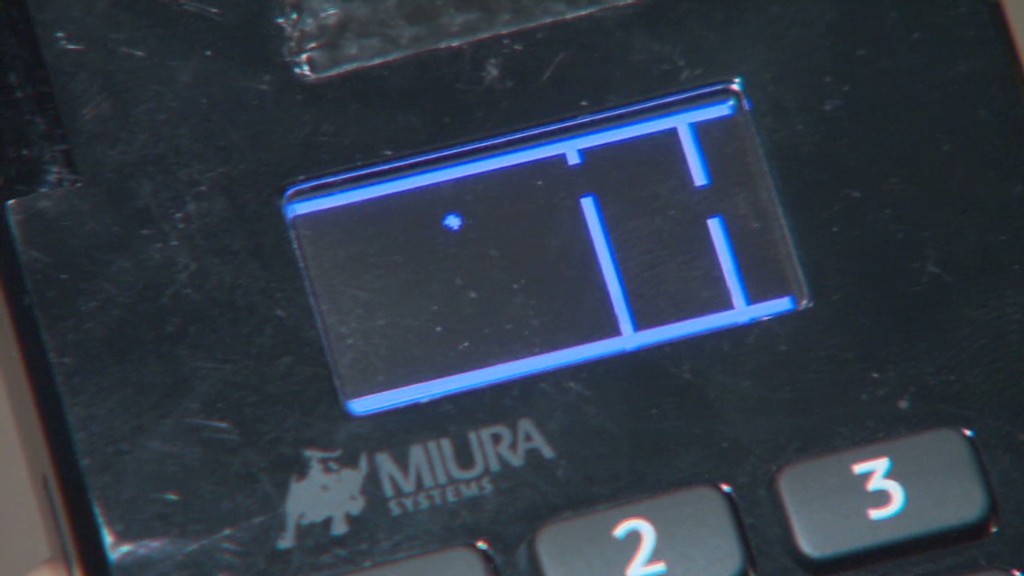
The passcode, set by default on credit rating card machines given that 1990, is easily observed with a speedy Google searach and has been uncovered for so extended you can find no sense in making an attempt to disguise it. It really is either 166816 or Z66816, depending on the equipment.
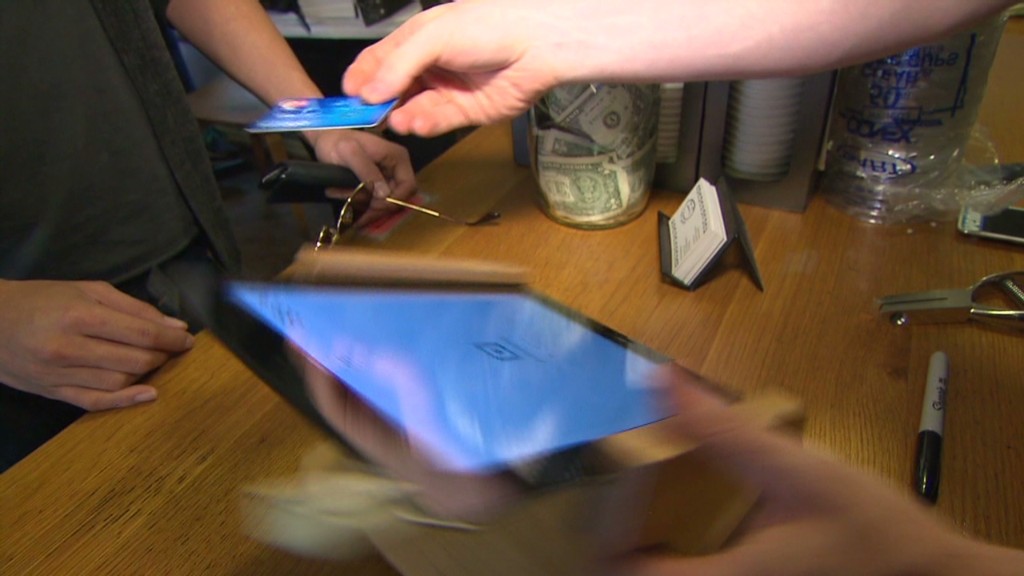
With that, an attacker can achieve finish command of a store’s credit score card viewers, likely allowing them to hack into the equipment and steal customers’ payment information (assume the Concentrate on (TGT) and Home Depot (Hd) hacks all about once more). No marvel big suppliers maintain shedding your credit history card data to hackers. Stability is a joke.
This most up-to-date discovery arrives from researchers at Trustwave, a cybersecurity firm.
Administrative obtain can be used to infect equipment with malware that steals credit card information, spelled out Trustwave government Charles Henderson. He specific his conclusions at final week’s RSA cybersecurity conference in San Francisco at a presentation known as “That Issue of Sale is a PoS.”
Consider this CNN quiz — find out what hackers know about you
The trouble stems from a video game of incredibly hot potato. Device makers market devices to unique distributors. These sellers promote them to shops. But no a single thinks it truly is their career to update the grasp code, Henderson advised CNNMoney.
“No a single is transforming the password when they set this up for the to start with time all people thinks the safety of their issue-of-sale is an individual else’s duty,” Henderson claimed. “We’re creating it fairly effortless for criminals.”
Trustwave examined the credit score card terminals at far more than 120 suppliers nationwide. That includes main outfits and electronics merchants, as very well as community retail chains. No distinct shops ended up named.
The extensive majority of equipment have been produced by Verifone (Pay). But the similar concern is present for all main terminal makers, Trustwave claimed.

A spokesman for Verifone claimed that a password alone just isn’t ample to infect devices with malware. The business explained, right until now, it “has not witnessed any attacks on the safety of its terminals based mostly on default passwords.”
Just in case, although, Verifone mentioned shops are “strongly advised to transform the default password.” And these days, new Verifone units come with a password that expires.
In any scenario, the fault lies with merchants and their special suppliers. It can be like household Wi-Fi. If you acquire a property Wi-Fi router, it really is up to you to alter the default passcode. Stores should be securing their very own equipment. And equipment resellers ought to be encouraging them do it.
Trustwave, which can help protect shops from hackers, reported that maintaining credit history card machines protected is lower on a store’s listing of priorities.
“Organizations expend additional dollars picking out the colour of the level-of-sale than securing it,” Henderson explained.
This difficulty reinforces the conclusion produced in a recent Verizon cybersecurity report: that suppliers get hacked mainly because they’re lazy.
The default password detail is a really serious issue. Retail laptop networks get uncovered to laptop viruses all the time. Take into consideration just one situation Henderson investigated recently. A horrible keystroke-logging spy software program ended up on the laptop a keep uses to procedure credit score card transactions. It turns out staff had rigged it to enjoy a pirated version of Guitar Hero, and unintentionally downloaded the malware.
“It displays you the level of obtain that a great deal of people have to the point-of-sale surroundings,” he said. “Frankly, it’s not as locked down as it ought to be.”
CNNMoney (San Francisco) To start with revealed April 29, 2015: 9:07 AM ET





More Stories
National Park Adventures: Find Hidden Gems in the Wild
National Park Adventures: Explore Majestic Landscapes
Journey into the Wild with National Park Adventures